7 Communication technologies revolutionizing the IoT
Updated on October 15,2022
Communication technologies revolutionizing the IoT
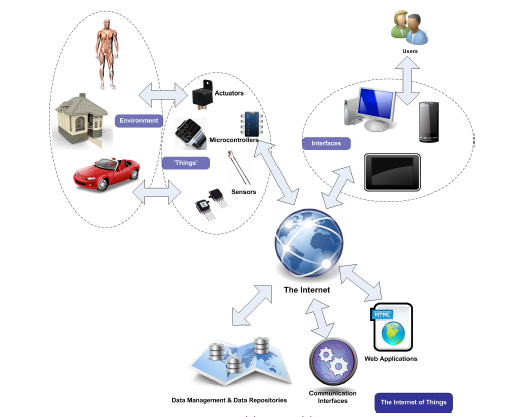
As discussed in an earlier article, the Internet of Things (IoT) can be summarized to co....
Read More
Updated on October 15,2022
Communication technologies revolutionizing the IoT
As discussed in an earlier article, the Internet of Things (IoT) can be summarized to co....
Read More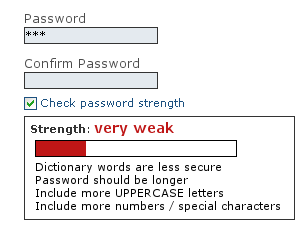
Updated on October 23,2022
We live in a password-centric world, where four and 20 characters are the difference makers in whether you can access your data, make your online p....
Read More
Updated on October 23,2022
Africa, generally, is to be counted among the lucky lot when it comes to cyber-attacks.
Africa isn’t that educated when it comes to h....
Read More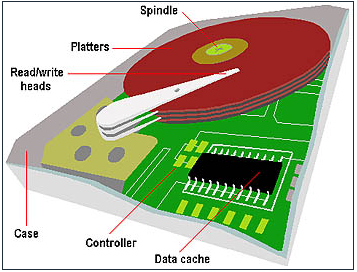
Updated on October 15,2022
The hard disk drive is the location on our computer where the applications, files, folders and other data are permanently stored. It is used by the....
Read More
Updated on October 15,2022
Allow me to begin with the literal definition of a password. A password is a string you use for validation in order to access a given resource (may....
Read More
Updated on October 15,2022
It’s amazing what technology can do. Just a click away is the world’s largest collection of knowledge. Knowledge that, if used wisely,....
Read More